| 구현기능 |
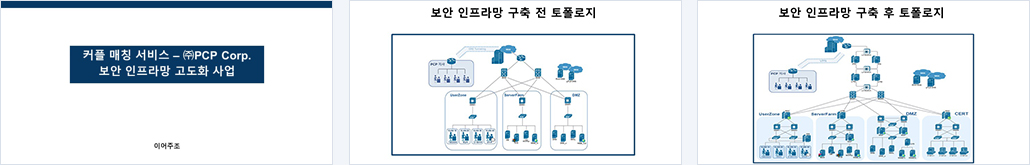
1. Network 관련 구성 내용
- Hierarchical 3 layer 모델을 기반으로 Network 토폴로지 설계
- ServerFarm, 관제센터 Network 망분리
- Network 할당 내역
- Spanning Tree, Gateway 이중화, VPN(Remote Access)
- L4 Switch(SLB, FWLB, HA)
2. 보안
iptables(Network 기반), IDS(Network 기반), IPS, NAC(Untangle)
3.System 관련 구성 내용
계정 및 그룹 관리, rsyslog, logrotate, 백업(rsync), PAM, Tripwire
4.Service(Application) 관련 구성 내용
DNS(Master, Slave), DNSSEC, DHCP, FTP, WEB(HSTS-Redirect)
5. 기타 SOL 관련 구성 내용
UTM ESM WAPPLES(proxy)
-----
[사용 기술]
1) White Box / Black Box Testing
2. 수동적 정보수집
1) DNS 정보수집
(1) Zone Transfer
(2) Dictionary Attack
2) 경로추적
3. 능동적 정보수집
1) Active Host Scanning
2) Port Scanning
3) IDLE Scanning(winxp)
4) Vulnerability Scanning (Window XP 대상)
5) Nessus (Window XP대상)
----------------------------------------------------------
4. 공격수행
1) Metasploit
2) Network
(1) Sniffing
- ARP Spoofing or ARP Redirect
- ICMP Spoofing(ICMP Redirect)
- GRE
- DHCP Attack(Starvation / Spoofing)
(2) Spoofing
- IP Spoofing(SSH 접근통제 우회)
- DNS Spoofing / DNS Cache Poisoning
(3) Hijacking
- TCP session Hijacking(Telnet)
3) System
(1) 악성코드
- Ransomeware, Trojan, RAT, Backdoor, Wiper Malware
(2) PW Cracking
- john-the-ripper, Hydra, Xhydra
4) WEB
(1) 정보수집
- Banner Grabbing, Fingerprinting, WEB Spidering, Vulnerability Scan
(2) Bypassing Client Side Validation
(3) WEB 인증 공격
- Form Based Authentication Brute Forcing
- Basic / Form Based Authentication Dictionary Attack
(4) WEB 세션 공격
- Fixation, Hijacking
(5) Cross Site Scripting
- Stored, Reflected
(6) Cross Site Request Forgery
- Stored, Reflected
(7) SQL Injection
- 인증우회, Non-Blind(Query/Error), Blind(Boolean/Time)
(8) Directory Listing
(9) File Upload/Download
(10) SSL Attack
- Mitm, Strip, HeartBleed
5) DOS / DDOS / DRDOS(실제공격)
(1) DOS
- Syn Flooding, TCP Connection Flood, UDP Flooding, ICMP Flooding
(2) DDOS
- TCP Connection Flood, UDP Flooding, ICMP Flooding, GET Flooding, Hulk, CC Attack, Slow HTTP POST/Header/read DOS
(3) DRDOS
- ICMP Flooding |













 KH IEI PROJECT
KH IEI PROJECT









 ③ 제1항에 따른 권리 행사는 정보주체의 법정대리인이나 위임을 받은 자 등 대리인을 통하여 하실 수 있습니다. 이 경우 개인정보보호법 시행규칙 별지 제11호 서식에 따른 위임장을 제출하셔야 합니다.
③ 제1항에 따른 권리 행사는 정보주체의 법정대리인이나 위임을 받은 자 등 대리인을 통하여 하실 수 있습니다. 이 경우 개인정보보호법 시행규칙 별지 제11호 서식에 따른 위임장을 제출하셔야 합니다.
 ④ 개인정보 열람 및 처리정지 요구는 개인정보 보호법 제35조 제4항, 제37조 제2항에 의하여 정보주체의 권리가 제한 될 수 있습니다.
⑤ 개인정보의 정정 및 삭제 요구는 다른 법령에서 그 개인정보가 수집 대상으로 명시되어 있는 경우에는 그 삭제를 요구할 수 없습니다.
⑥ KH정보교육원은 정보주체 권리에 따른 열람의 요구, 정정·삭제의 요구, 처리정지의 요구 시 열람 등 요구를 한 자가 본인이거나 정당한 대리인인지를 확인합니다.
④ 개인정보 열람 및 처리정지 요구는 개인정보 보호법 제35조 제4항, 제37조 제2항에 의하여 정보주체의 권리가 제한 될 수 있습니다.
⑤ 개인정보의 정정 및 삭제 요구는 다른 법령에서 그 개인정보가 수집 대상으로 명시되어 있는 경우에는 그 삭제를 요구할 수 없습니다.
⑥ KH정보교육원은 정보주체 권리에 따른 열람의 요구, 정정·삭제의 요구, 처리정지의 요구 시 열람 등 요구를 한 자가 본인이거나 정당한 대리인인지를 확인합니다.





